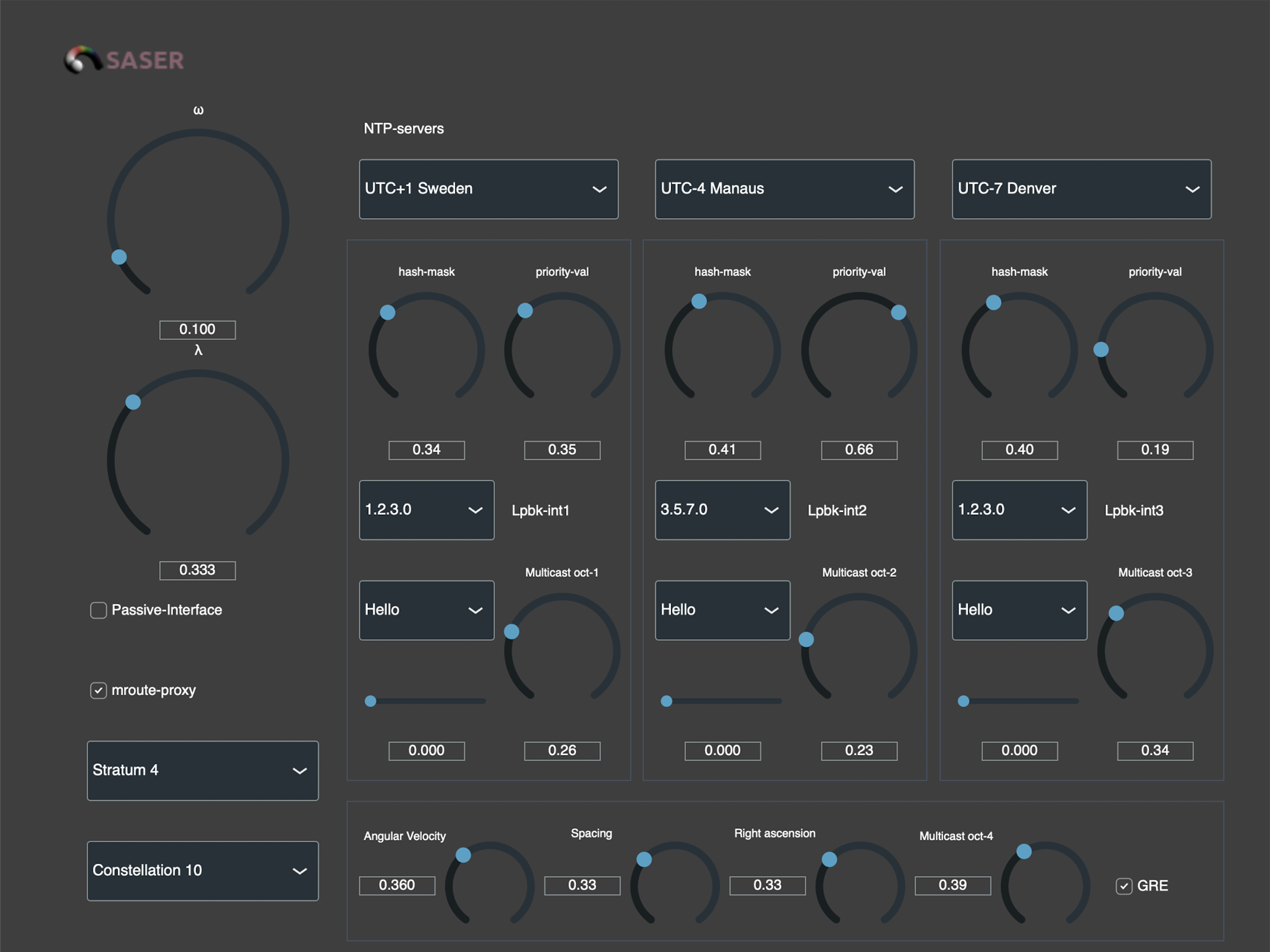
My cyberairplanes “Traitor” is a cyberairplane. A phone equipped with SASER is a cyberairplane control equipment. To date, I have three models of cyberairplanes: “Traitor”, “Dart” and “Black Shark”. They correspond to their own control equipment. Let’s start with “Traitor.” The heavy reconnaissance forwarder “Thor” has the ability to holography. It has an autopilot mode that is controlled by the…